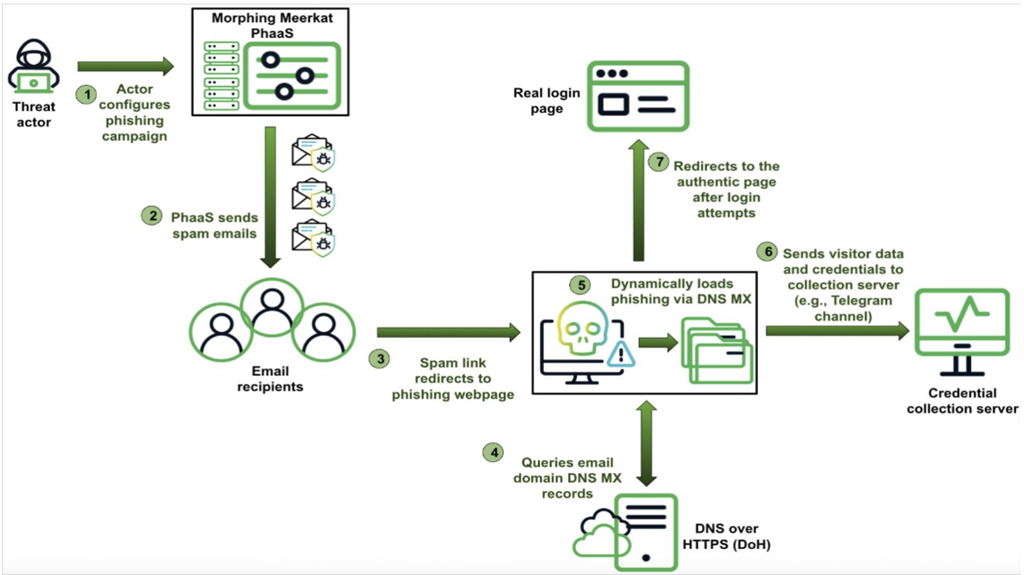
Researchers at Infoblox have published a report describing a Phishing-as-a-service (PhaaS) kit observed in use since 2020, that has grown in complexity and among other capabilities now abuses domain name server mail exchange (DNS MX) records to “dynamically serve phishing web templates that relate to the victim’s email service,” targeting users globally and in over a dozen languages. Referencing Cloudflare DNS over HTTPS (DoH) or Google Public DNS, the kit loads one of at least 114 spoofed HTML templates mimicking a login page relevant to the victim. Infoblox suggests organizations strengthen DNS security, “tightening DNS control so that users cannot communicate with DoH servers or blocking user access to adtech and file sharing infrastructure not critical to the business,” positing that “if companies can reduce the number of unimportant services in their network, they can reduce their attack surface.” Heath Renfrow, co-founder and CISO at Fenix24, recommends deep DNS logging and analysis; monitoring for brand spoofing and MC record anomalies; using zero-trust gateways; enforcing DMARC, DKIM, and SPF authentication; and requiring regular anti-phishing training. More https://blogs.infoblox.com/threat-intelligence/a-phishing-tale-of-doh-and-dns-mx-abuse/
Phishing-as-a-Service Kit Reads DNS MX Records
- Post author:System
- Post published:4 April 2025
- Post category:Blog & News